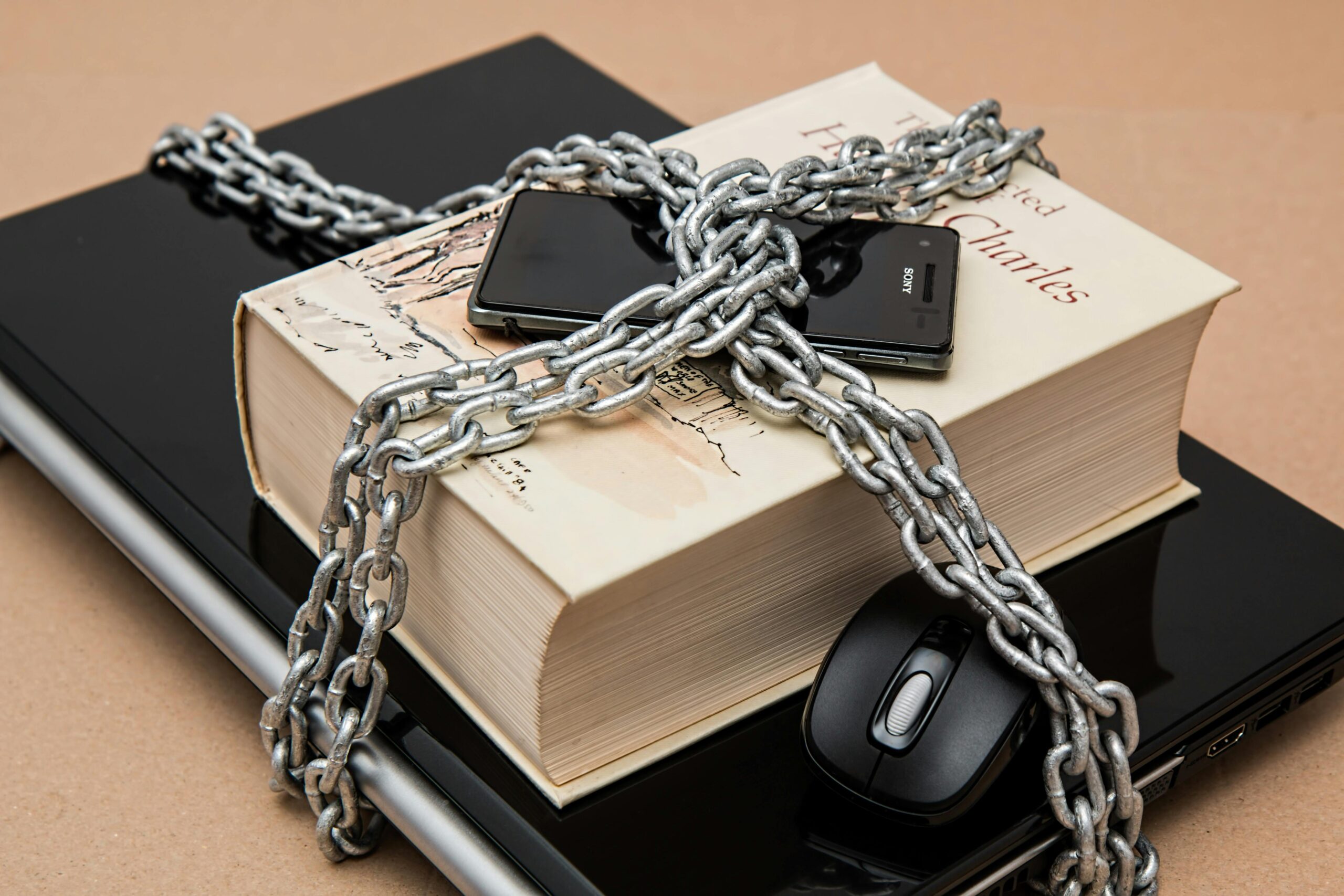
Guard Your Data with Chain Precision
In today’s digital landscape, protecting sensitive information requires more than just strong passwords and firewalls—it demands a comprehensive approach to data integrity through proper chain-of-custody protocols. 🔐 Understanding Chain-of-Custody in Digital Environments Chain-of-custody represents the chronological documentation and paper trail that records the sequence of custody, control, transfer, analysis, and disposition of physical or electronic … Ler mais